At a glance
Even before the pandemic, trends such as the cloud computing boom had led to the emergence of new security challenges and solutions. Now, however, the shift to remote and hybrid workforces has demolished what was left of the traditional defence “perimeter” – the office network.
The pressure is on companies to enable employees to work flexibly and securely from home or the office.
In previous INTHEBLACK issues, we explored the challenges businesses face in enabling flexible hybrid working. These included ensuring employees have the digital infrastructure (see the March 2022 and April 2022 issues of INTHEBLACK).
However, enabling employees to work securely from anywhere is, if anything, an even bigger challenge. Findings of the State of Hybrid Workforce Security 2021 research report by cyber security firm Paolo Alto show half of organisations compromised on risk mitigation and security controls to enable remote access for employees.
How can businesses turn that around and secure their highly distributed networks?
Antivirus apps
It starts with securing “endpoints” – the computers and other devices accessing business data. Antivirus software is the bare minimum.
Fortunately, most antivirus tools – including Microsoft Defender, which comes free with Windows – are very effective at protecting systems from malware, according to recent anti-malware test results by AV-TEST, an independent organisation that evaluates and rates antivirus and security suite software for Microsoft Windows and Android operating systems, according to a variety of criteria.
While Microsoft Defender performed well in these tests, others scored even higher.
Some of the better performers included products from Avast, AVG, Avira, Bitdefender, ESET, FireEye, F-Secure, G Data, Kaspersky, Norton, Sophos, Symantec and Trend Micro.
For example, in Table 1 we’ve listed the consumer security apps that achieved 100 per cent detection and protection rates and top-scored in AV-TEST’s performance and usability testing.
In addition to top-notch malware protection, these commercial apps offer worthwhile extra features, such as online banking and payments protection, a password manager and virtual private network (VPN).
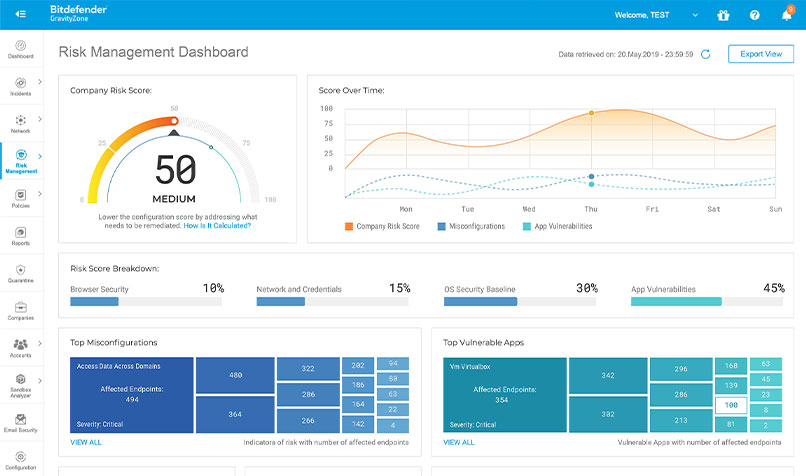
Endpoint security and controls
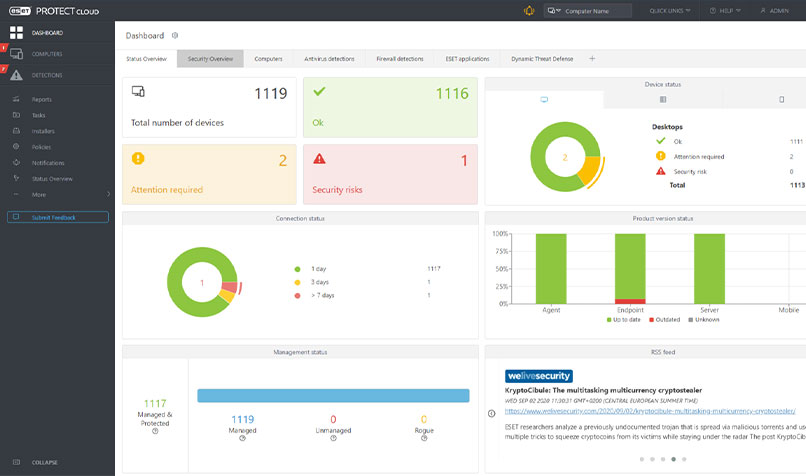
For even better security across the company, consider upgrading to business-grade endpoint protection. These solutions provide management tools, ensuring every device accessing business data has up-to-date antivirus software.
They also provide multi-layered protection, including allowing you to identify risks such as vulnerable apps and devices.
Table 2 includes the endpoint protection apps that achieved 100 per cent detection and protection rates and top-scored in performance and usability in AV-TEST’s results.
Alternatively, endpoint detection and response solutions from the likes of Bitdefender and Symantec go further with more advanced tools to detect and contain security incidents, and provide guidance on how to resolve the problem.
Minimising "attack surfaces"
Protecting endpoints is just the start, however. Businesses need to guard other “attack surfaces” that cybercriminals target.
Malicious emails are still a huge threat, for example, and services such as MailGuard use advanced filtering techniques to prevent these emails reaching employees.
User log-in credentials are another favourite target of hackers. The likes of 1Password for Business can ensure your employees use secure passwords, along with multi-factor authentication when signing into apps.
Identity and access management tools such as Okta and OneLogin go further with more sophisticated controls over access to apps and data. These include single sign-on to allow users to easily and securely access multiple apps, along with device management controls.
A single cloud-based enterprise solution
For larger or more security-conscious organisations, there is a bevy of advanced tools and techniques to consider.
For example, data loss prevention solutions such as Digital Guardian inspect network data and traffic to help prevent sensitive information from leaving an organisation.
However, these advanced security tools are increasingly being bundled into secure access service edge (SASE) solutions that are typically integrated with a software-defined wide-area network platform.
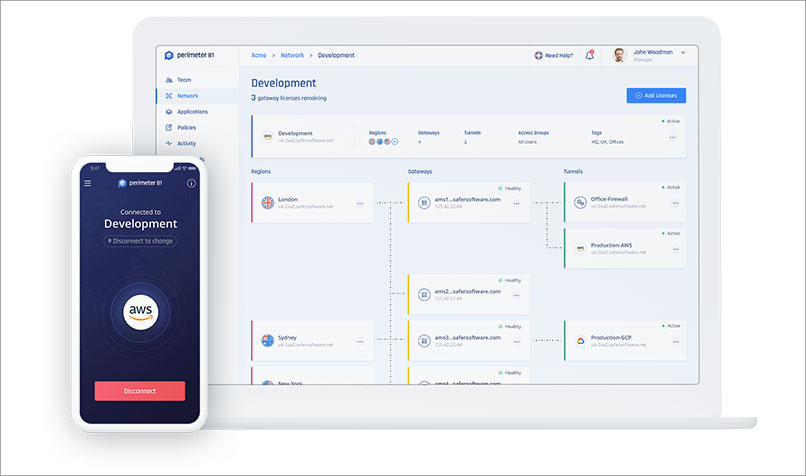
Perimeter 81, for example, combines network controls and security tools in a cloud-based SASE service. Importantly, it provides security at a network level with strictly enforced identity-based controls over access to apps and data.
Like most other enterprise security vendors, Perimeter 81 supports a “Zero Trust” approach that requires all users to be authenticated and continuously validated when accessing business apps and data. As such, this approach requires a range of tools and techniques, such as identity-based access policies, network monitoring and traffic encryption.
Among other benefits, Zero Trust frameworks are seen as a logical replacement for enterprise VPNs, which many security experts see as no longer up to the task of protecting modern networks supporting hybrid workforces.
Table 1 : Consumer security apps with perfect AV-TEST scores
| Windows | MacOS | Android |
|---|---|---|
| ESET Internet Security | Avast Security | Avast Mobile Security |
| F-Secure SAFE | AVG AntiVirus | AVG AntiVirus FREE |
| Kaspersky Internet Security | Avira Security | Bitdefender Mobile Security |
| Norton 360 | Bitdefender Antivirus | G DATA Mobile Security |
| F-Secure SAFE | Norton 360 | |
| Norton 360 | Trend Micro Mobile Security | |
| TrendMicro Antivirus |
Table 2 : Business security apps with perfect AV-TEST scores
| Windows | MacOS |
|---|---|
| Bitdefender GravityZone | Bitdefender GravityZone |
| ESET PROTECT | ESET PROTECT |
| F-Secure Elements Endpoint Protection | FireEye Endpoint Security |
| Kaspersky Endpoint Security | Sophos Endpoint |
| Symantec Endpoint Protection | Symantec Endpoint Protection |